improve your it services
Our Mission
Our mission is crystal clear – your digital safety. In an age where the virtual realm is an integral part of our lives, ensuring your peace of mind is our top priority. We understand the gravity of the challenges that come with living in a hyper-connected world where the importance of cybersecurity cannot be overstated.
main features of it services
Your online safety is our top priority. Benefit from cutting-edge security measures that protect your data, identity, and transactions. We employ state-of-the-art encryption and multi-layered security protocols to keep you safe.
- Scalability
- Cost Efficiency
- Cybersecurity
- Reliable support
- Enhanced Productivity
- Access to Expertise
Enhanced Productivity: IT services help streamline processes, automate repetitive tasks, and improve efficiency. This, in turn, boosts overall productivity within an organization as employees can focus on more value-added tasks.
Cost Efficiency: Managed IT services often provide cost-effective solutions compared to hiring in-house IT teams. Outsourcing IT services eliminates the need for full-time staff, training, and infrastructure expenses.
Cybersecurity: IT services offer robust cybersecurity measures to protect against data breaches and cyberattacks. This ensures the safety of sensitive information and prevents costly security incidents.


Scalability: IT services can quickly scale up or down to meet the changing needs of a business. This flexibility is essential for companies experiencing growth or seasonal fluctuations in demand.
Access to Expertise: IT service providers typically have highly skilled professionals with expertise in various domains of technology. This access to specialized knowledge and experience is invaluable for troubleshooting and strategic planning.
These benefits make IT services an essential component of modern businesses, enabling them to stay competitive, secure, and efficient in a rapidly evolving technological landscape.
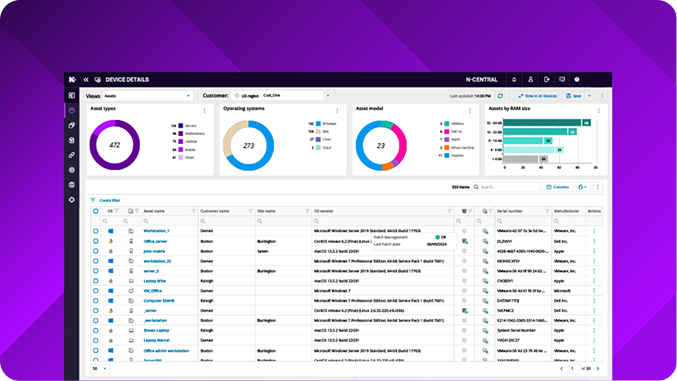
Unified Endpoint Management
Patch & Vulnerability Management
Security Management with EDR, XDR, MDR
Cloud User and Asset Management
How does N‑central take the pain out of routine workloads?
By simplifying automation of repetitive tasks, eliminating notification fatigue, and providing tools designed for efficiency and innovation.
- Get to full network visibility faster by scanning and importing Windows, Mac OS, Linux and network devices in minutes.
- The Infinity Core alleviates the heavy lift and human errors of deploying and configuring endpoint standards, optimizing for your ideal state.
- Execute vital workloads like patching OS, third parties apps, and security vulnerabilities with minimal hands-on management.
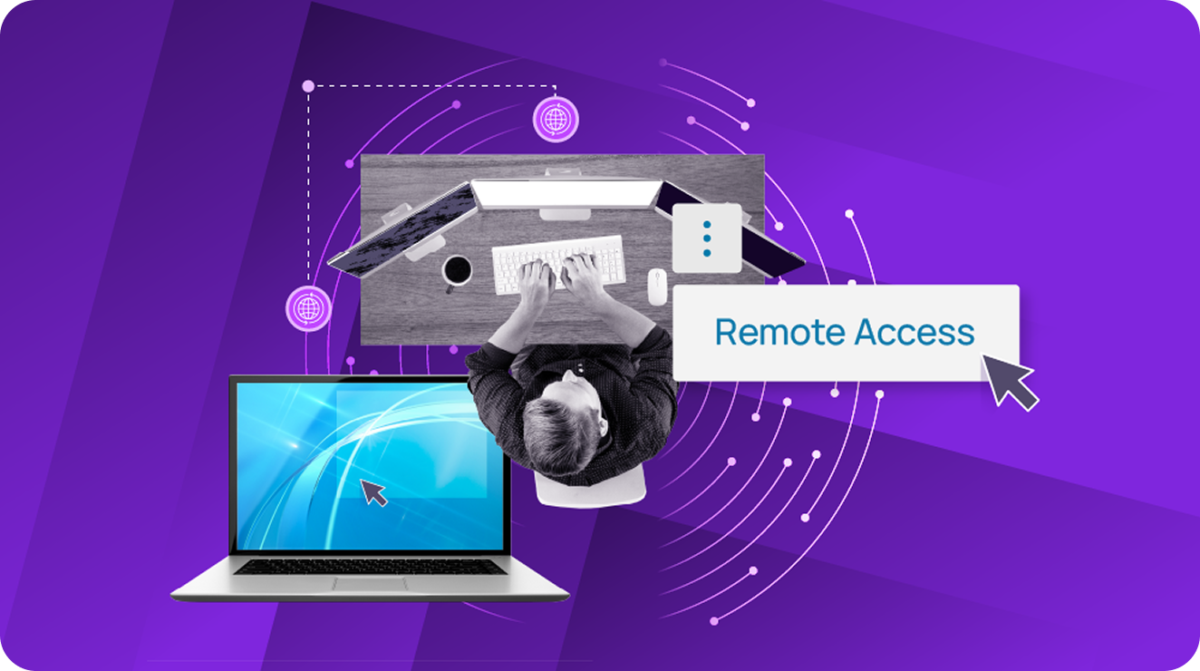
Remote Access
- Manage servers, workstations, mobile, and networks (Windows, Mac, and Linux)
- Chat directly without needing a remote session
- Troubleshoot with device information and specs at your fingertips
- Quickly connect to new devices and users using a simple PIN
- Remote background access to devices to avoid disrupting users
- Complete audit trail and session summary details
- Support toolkit for everyday common scripts
Network Device Monitoring
- Monitor all types of network devices including Cisco, Fortinet, HP, Juniper, SonicWALL, and more
- Manage devices with Secure Shell (SSH) and automation
- Create custom monitoring for any MIB enabled network device
- View Network devices alongside user and server devices

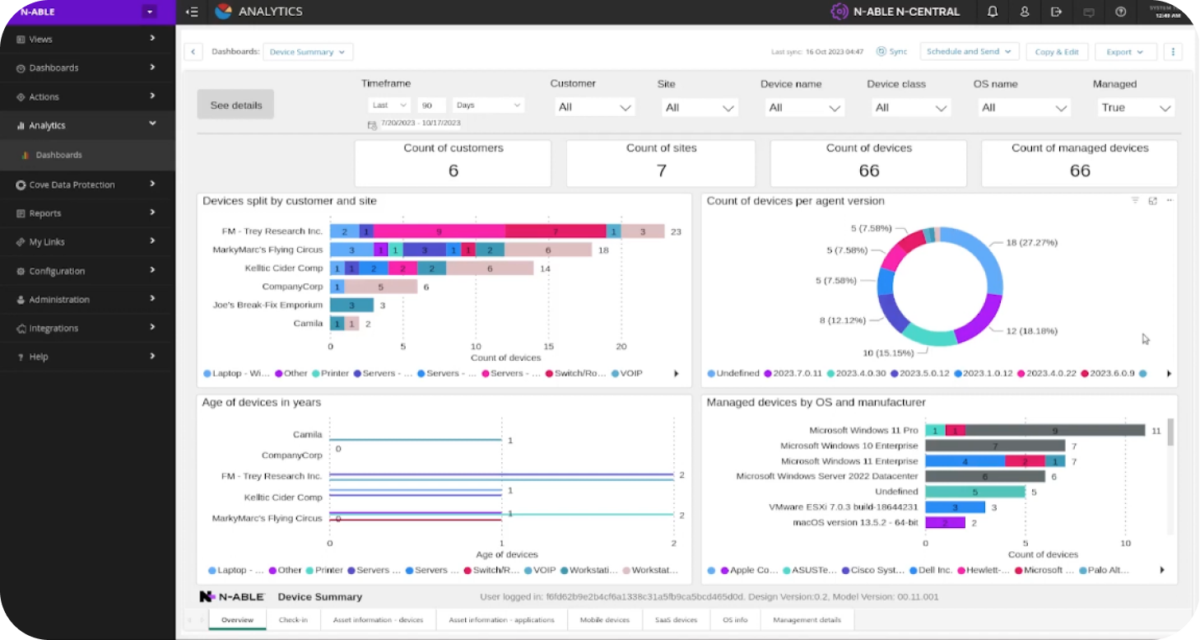
Make more informed decisions thanks to N‑central business intelligence
Take a quick look into the Analytics and reporting capabilities of N‑central. You get a view into the types of dashboards and reports available, as well as the powerful BI tools N‑central partners have to make better decisions for their business.